 IRSF- International Revenue Share Fraud
IRSF- International Revenue Share Fraud
This week we have David Cargill as guest editor. David runs the Operations Working Group at the Internet Telephony Sevice Providers’ Association (ITSPA) and takes a special interest in VoIP Fraud. David has invited a number of experts to contribute guest posts on fraud related subjects. This ties in with the ITSPA/trefor.net Workshop on Wednesday that has VoIP fraud and WebRTC as its main themes. This is his second choice of post, in which IRSF is discussed, is written by Colin Yates, Managing Director of Yates Fraud Consulting Limited:
The telecommunications industry has a huge gap between those operators who manage fraud effectively and those who do not. Those who are effective fraud managers, whether they are a Tier 1, 2 or 3 operator, are generally those who have matured over the years with a strong mandate and support from their Executive to do the job, while being provided with the necessary budget, resources and tools to do it well. Some senior management unfortunately view fraud losses simply as a cost of business, and allocate very little budget and resource to it. In these cases fraud losses are generally not measured or reported, so will remain unknown and not reflected in quarterly, half yearly or annual financial reporting.
There are some CSP’s who have enjoyed reputations within the industry as leaders in the management of fraud, but over time these reputations have diminished and their fraud losses have increased. Some of this could be blamed on a change of senior leadership who failed to appreciate the importance of effective fraud management. This could also be a result of a fraud manager who failed to continually make it clear to the organisation how much value they were adding to the business by effectively managing fraud. An effective Fraud Manager will take whatever steps are necessary to ensure that the papers for every Board meeting will include his quarterly fraud report to clearly identify the fraud recoveries and averted losses they have achieved during the period since the last meeting.
Fraud within Telecom operators is generally measured as a percentage of total revenue, and depending on which organisation is providing the figures, this could be estimated at anywhere between 1% and 5% of total revenue. In my experience an operator with a mature fraud team with the necessary fraud detection/prevention tools, along with the support of his management team is likely to maintain their fraud losses at under 0.50%. Assuming this is a tier 2 operator with total revenues of $US1.5 billion, if the effectiveness of the fraud team was permitted to deteriorate to a point where fraud losses increased by another 0.25% of total revenue, this would add a further $US3.75 million to the annual fraud losses. To recover this revenue through adding new customers would require upwards of 10,000 new customers to be added to the business, assuming an average ARPU of around $US370 per year. Would it not make better business sense to continue to support the fraud management function with resources and tools at a cost of probably 10% of the additional fraud losses suffered.
Subscription fraud is without a doubt the biggest contributor to fraud losses across the industry. While most operators would agree that their aggregated subscription fraud loss far exceeds those suffered by any other fraud type, the drive to attract and connect new customers can make it difficult to manage. Most sales channels will require that a potential customer who meets basic identity verification checks will be provided service during that one visit to a physical or on-line store. Without investment in real time subscription fraud detection tools, this type of fraud is always going to be difficult to manage. Some of these tools are no longer expensive and can allow a CSP to take more risk when providing service to new customers.
International Revenue Share Fraud (IRSF)1 has to be regarded as the one fraud type that the industry has failed to manage effectively, primarily again because of a lack of investment in tools and resources by some to prevent and detect an attack early to minimise losses. IRSF Fraudsters can attack a business using many enablers, for example subscription fraud, roaming Fraud, PBX hacking, Mobile Malware, Wangiri Fraud and others. Some CSP’s use tools, either developed in-house or obtained from an FMS provider and do manage their IRSF risk effectively, but many others simply operate in the belief that this fraud will never impact them, so they will make no investment in a defensive strategy, and simply take the risk. This decision is typically not taken by those accountable for managing fraud, but by those a level or two above who control the budgets. In most cases, this decision maker will have no idea what the actual risk is, and the impact of not implementing these controls may result in losses way above his delegated financial authority. It is still not unusual to hear of IRSF losses that have amounted to over $US500,000 in a 2 or 3 day period. An investment of under $US30,000 could have avoided most of these losses.
It is well documented now that around 85 to 90% of all IRSF incidents occur in the period between Friday evening and Monday morning when many CSP’s fraud monitoring staff are not in the office. Unfortunately even some of those who have made the investment in monitoring tools will continue to ‘take the risk’ over weekends and will not take that monitoring a step further to enable some automation, or diversion of outputs from their monitoring systems to a 24×7 activity within their business. In a roaming situation, NRTRDE (high roaming usage) records are delivered within 4 hours of a roaming call completing, and this includes the period right through the weekend. Having made an investment to implement this fraud control, it is hard to understand why no-one would be looking at these in real time to identify fraud, or have some automated process set up to manage an obvious fraud indicator.
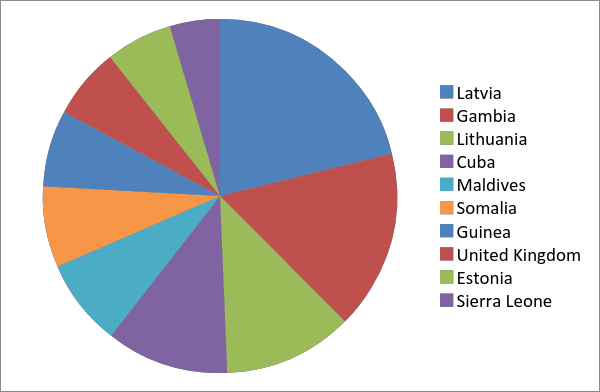
Without effective monitoring tools, some operators will simply block what they consider are high risk destinations assuming that this will reduce their risk of becoming a victim to IRSF. We currently monitor destinations and numbers used for IRSF and the total Countries advertised by IPRN Providers number 221 and the test numbers we have recorded in to these countries number over 100,000. However the top 10 high risk destinations very seldom change and are as indicated in the graph below. These 10 destinations are responsible for 50% of the IPR numbers being advertised, but any of the remaining 211 country International Revenue Share numbers advertised could result in significant fraud losses being suffered.
Fortunately there are more and more operators who have identified the value of 24 x 7 fraud monitoring, and have managed to make the argument for resources and tools to allow this compelling enough to obtain sufficient budget to implement this strategy.
Unfortunately this has not resulted in a reduction of the overall IRSF problem. It has simply driven the fraudsters to look for easier targets and these are currently smaller MNO’s and more recently MVNO’s. Fraudsters have come to realise that many MVNO’s do not have Fraud Management expertise in-house, or access to the information and networking industry forums that most MNO’s have available to them.
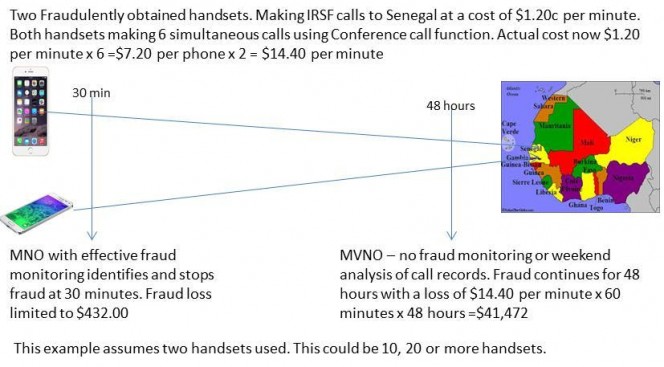
Prevention and Detection are the fundamentals of Fraud Management, which is particularly relevant for the telecommunications industry. The costs of pursuing a fraud strategy based on implementing the resources and tools required to monitor network usage are insignificant when compared to the likely losses you will suffer if you simply rely on luck. Anyone with any doubt in this area should arrange for an independent contractor to come in to their business and conduct a fraud risk review so that the full extent of the risks can be identified. A simple example of an MNO with an effective fraud monitoring process in place identifying and stopping an IRSF attack within 30 minutes, compared to an MVNO with no fraud process, allowing an IRSF attack to continue for 48 hours before detection, is demonstrated in the diagram below.
IRSF has now been around for at least 10 years in some form or another. Some CSP’s have lost significant amounts of money to it, and some fraudsters have generated small fortunes in fraudulent income from it. Many customers have been impacted through bill shock after their handset has been stolen or their PBX hacked, and many small countries have suffered social and economic impact as a result of their number ranges being hijacked by these fraudsters.
The argument for effective prevention and detection initiatives is compelling, but this does require some support and investment by an MNO or MVNO’s senior management team. After around 10 years of suffering from this fraud, it should be apparent that the various industry groups who have been searching for solutions are unlikely to come up with anything positive in the next year or two, so it really is up to the individual operators to take action to protect themselves.
1IRSF involves fraudsters calling international numbers that attract a high termination rate, from a stolen or fraudulently obtained connection, with an intention to inflate traffic in to those numbers and be paid a per minute fee from a number provider for each call made. Payment for these calls will eventually be required from the originating network, who will have no hope of recovering these costs.
Colin Yates is a telecommunications professional with over twenty five years’ experience, specifically in the area of fraud, investigations, RevenueAssurance and threat management. Colin specialises in the areas of Telecoms Fraud (Internal and External) and Investigations. He also has considerable experience with Personnel and Physical Security, Law Enforcement Agency Liaison,Intelligence Management, Regulatory Compliance, Revenue Assurance and Policy development.
Check out his website at www.yatesfraudconsulting.com. Also check out our other VoIP fraud posts here.
Read yesterday’s post on PABX fraud by Manuel Basilavecchia here