Is encryption the answer to data loss? Voipfone CEO Colin Duffy thinks not
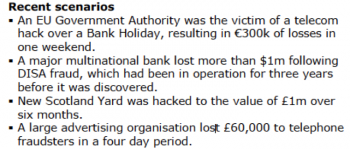
The TalkTalk hack and subsequent data loss – and to a lesser extent the Vodafone hack only a few days later – bring the issue of data security and telecommunications into the news. In the media, much emphasis has been placed on the use of encryption as a line of defence against data loss. This is only very partially true – encryption is not a panacea.
When it is useful, the system has already been compromised, the data is already lost and can be worked on at the criminal’s leisure or sold on to more sophisticated criminals with the tools to decrypt it. Encryption is not perfect and through cryptanalysis it can be broken. For example, knowing that you are looking at a list of tens of thousands of postcodes that are encrypted with the same key can provide sufficient information to decrypt the entire list. Moreover, the encryption key itself then becomes a prime target for hackers.
Encryption is most useful when it is used to protect data transport over a hostile medium e.g. when data is exchanged between two parties over the Internet or a laptop being taken out of the office or situations where physical hardware can be stolen.
But inside private networks it is far less useful. This is because customer data is in constant use by multiple users – for billing, reporting, and customer support and by customers for updates and information. Customer databases need multiple entry points and authorisations for both human and machine access. Encrypted information is unencrypted on the fly by the computer which processes it. If the hacker gains access to that computer as a user the data is automatically unencrypted and visible.
Any breach that allows an attacker access to a component such as remote code execution and login access would also give them access to the encrypted data and the encryption key. There are very few remote attack forms where encryption would prevent data loss once the hacker has penetrated the system.
In these circumstances, encrypting data adds extra load on processors and systems, adds system and managerial complexity and cost and mostly does little more than provide a false sense of security. In reality, encryption of data inside networks is of most use not for the protection of the data, but from subsequent media accusations of security laxness.
Finally, encryption does not protect against the database deletion or interference.
For a limited number of risks, data encryption can bring some security value to a system, but for most it has no benefit whatsoever. Therefore it certainly isn’t a replacement for the other security measures – protecting access to systems, minimising SQL injection or code execution vulnerabilities. It has to be considered a last line of defence, added on top of all other reasonable measures.
Colin Duffy www.voipfone.co.uk
This week of telecoms fraud posts is edited by Manuel Basilavecchia of Netaxis.